You can think of the Espionage Act as a law built for wartime, then left on the books for peacetime. It was born in World War I, designed to protect military operations and national defense information. A century later, it is still one of the government’s main tools for prosecuting the unauthorized retention or disclosure of sensitive national defense material. In practice, prosecutions most often focus on leakers and people with access or custody, not traditional news organizations acting as publishers.
That longevity creates friction. The Constitution explicitly protects speech and a free press. The Espionage Act, in several of its most important provisions, does not require proof that the public was actually harmed. The tension lives in that gap: a statute aimed at preventing damage versus constitutional principles built to tolerate risk in order to keep democracy open.

Join the Discussion
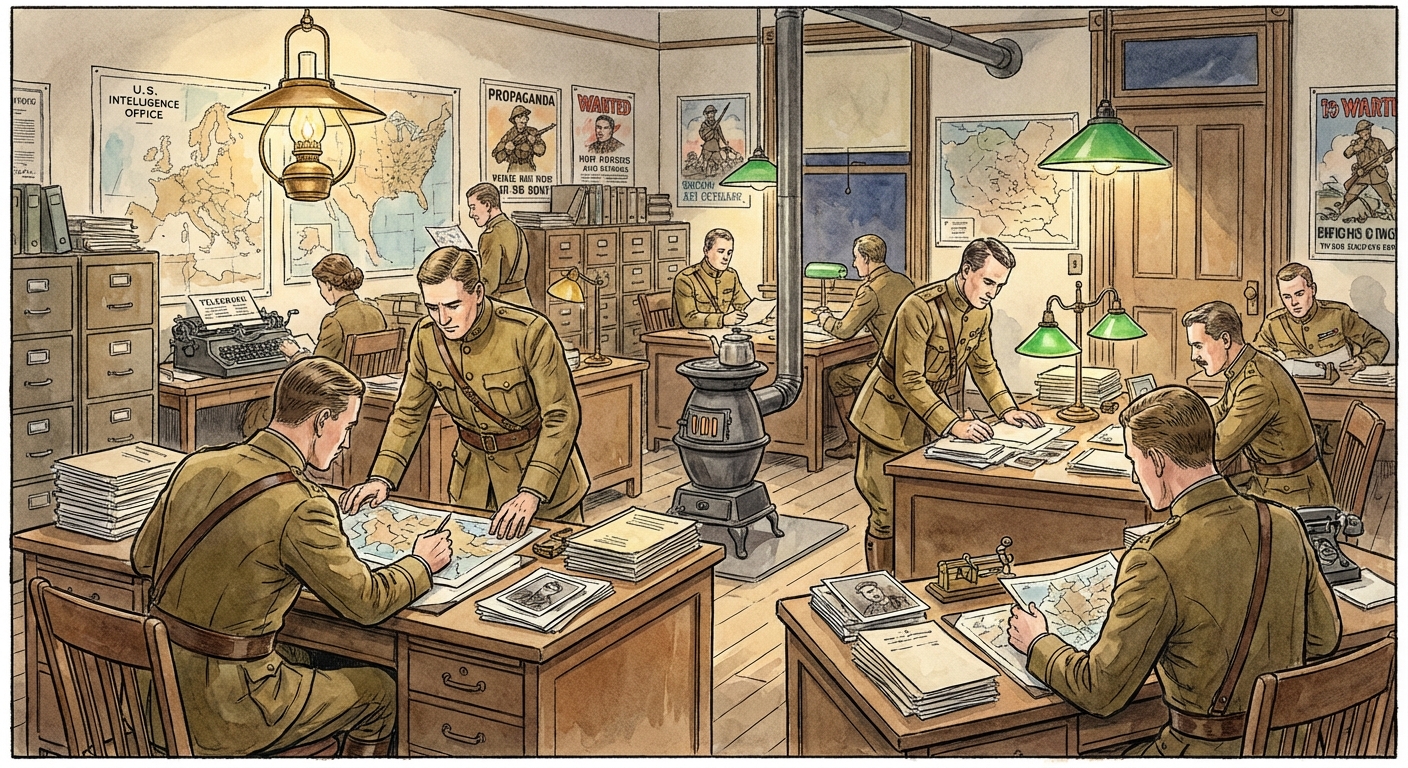
Where the Espionage Act came from
Congress passed the Espionage Act in 1917, shortly after the United States entered World War I. Its original purpose was straightforward: prevent interference with the war effort, stop spying, and deter the disclosure of information that could help enemy powers.
But the statute did not remain frozen in 1917. Over time it was expanded, amended, and repurposed. Some provisions focused on classic espionage, meaning working with or for a foreign power. Others reached broader conduct such as obtaining, retaining, or communicating “national defense information,” even when the case looks less like a spy story and more like a dispute over control of sensitive materials.
This matters because people often hear “Espionage Act” and assume the government must prove spying for an enemy. In many modern charges, that is not the required showing.
The law’s basic structure
The Espionage Act is not one single crime. It is a cluster of offenses, codified across several federal statutes. The provisions most commonly referred to as the Espionage Act are in 18 U.S.C. §§ 793 to 798, with related espionage offenses also appearing nearby in the code (including § 792 and § 794).
Three broad buckets help orient the statute:
- Traditional espionage: conduct tied to aiding a foreign government or harming the United States.
- National defense information offenses: obtaining, retaining, or sharing closely held defense-related information without authorization, even without proof of foreign agency.
- Communications intelligence protections: special protections for communications intelligence (COMINT) and certain cryptographic information, often charged under 18 U.S.C. § 798.
Core offenses charged today
Modern Espionage Act cases frequently rely on provisions focused on national defense information, especially 18 U.S.C. § 793(d) and § 793(e) (handling, retention, and transmission) and, in the communications intelligence context, § 798.
These cases most often involve government employees, military personnel, and contractors, but they can also involve outsiders in “receipt” scenarios. The legal posture can shift depending on whether someone had authorized access at the start, received the material from someone else, or took steps to obtain it without authorization.
1) Unauthorized retention or failure to deliver
One widely used theory involves a person who has unauthorized possession of national defense information and:
- willfully retains it, and
- fails to deliver it to an officer or employee of the United States entitled to receive it.
This is where the Act can look less like classic espionage and more like a high-stakes dispute over custody and control. The government’s focus is often: what was the information, did the person have lawful authority to keep it, and did they knowingly keep it when they should not have.
2) Unauthorized transmission or communication
Another common provision covers willfully communicating, delivering, transmitting, or causing national defense information to be communicated to someone not entitled to receive it.
In plain English: even if you obtained the information lawfully at first, the crime can be in the sharing. The audience matters. Authorization matters. The identity of the recipient may matter for sentencing and narrative, but the core statutory question is entitlement and willfulness.
3) Obtaining with harmful intent
Some Espionage Act provisions do look like the classic espionage model. They focus on obtaining or delivering information with intent or reason to believe it will be used to injure the United States or aid a foreign nation. Those provisions tend to align more closely with the word “espionage” as most people use it.
What prosecutors must prove
Each charged section has its own elements, but modern Espionage Act prosecutions often revolve around a few recurring legal concepts. These are the hinges a case swings on.
“National defense information” (NDI)
The statute uses the term “national defense,” not the modern bureaucratic term “classified.” Courts generally treat NDI as information that is closely held by the government and that, if disclosed, could be potentially damaging to U.S. national security or advantageous to a foreign nation. The exact phrasing and emphasis can vary by circuit and by the specific charge, but the “closely held” and “potential harm” ideas show up again and again.
Two practical consequences follow:
- Classified markings are powerful evidence, not the legal definition. Classification often supports the government’s argument that information was closely held and sensitive, but courts still ask whether the material fits the statute’s NDI framework.
- Unmarked does not automatically mean unprotected. Some defense-related information can be treated as NDI even without formal classification stamps if it is closely held and disclosure could be damaging.
Authorization and “entitled to receive”
Many charges rise or fall on whether the defendant was authorized to possess or share the information, and whether the recipient was “entitled to receive” it. That entitlement can involve clearance, role, need-to-know, or lawful authority, depending on context.
Willfulness and knowledge
Several provisions require that the defendant acted “willfully.” In this context, willfulness generally means more than a mistake. Courts often frame it as an intentional violation of a known legal duty, or at least proof that the defendant understood the handling was unlawful and chose to do it anyway. The precise articulation can vary by provision and jurisdiction.
Harm is often not an element
In many prosecutions, the government does not need to prove that actual damage occurred, only that the information was of a type whose disclosure could be damaging and that the defendant knowingly handled it in a prohibited way. That design is part of why the Act remains controversial in speech and press contexts.
How it differs from mishandling laws
In public conversation, “mishandling” is often used as a catch-all for any improper treatment of sensitive materials. Legally, there is a difference between the Espionage Act and other statutes that target records management, removal, or negligent handling.
Espionage Act: defense information
The Espionage Act centers on the nature of the information and the risk it poses to national security. It can apply even if the conduct is framed as retention or disclosure without classic spy motives.
Other laws: records, obstruction, systems
Other federal laws may come into play when the allegation is about:
- Government records: improper removal, concealment, destruction, or failure to preserve records.
- Obstruction: interfering with an investigation, a subpoena, or lawful retrieval efforts.
- Unauthorized access or computer misuse: accessing systems without authorization or exceeding authorized access.
- Negligent handling in specific contexts: certain statutes punish gross negligence or mishandling of particular categories, though these are narrower and fact-dependent.
The key distinction is that records statutes are often about custody and preservation, while Espionage Act charges are often about national defense sensitivity and unauthorized possession or disclosure.
Why First Amendment tension persists
The First Amendment protects speech, press, and the right to receive information. The Espionage Act protects national defense information by criminalizing certain acquisition, retention, and disclosure. When those two principles meet, the conflict is not theoretical. It is structural.
Speech versus conduct
Courts generally recognize a difference between:
- speech as expression and publication, and
- conduct such as theft, unauthorized access, breach of duty, or unlawful retention.
The harder cases live in the middle, where publishing true information intersects with government claims of secrecy and security.
Prior restraint versus punishment
In First Amendment law, blocking publication in advance is treated as an extraordinary step, historically disfavored. The Espionage Act is more often used as a tool for criminal punishment after information is retained or disclosed, rather than a mechanism to pre-approve speech. That difference shapes how courts analyze disputes involving the press and national security.
Public interest is not a built-in defense
A recurring civic question is whether exposing wrongdoing should excuse disclosure of sensitive information. Morally, people may answer yes. Legally, the Espionage Act is not written as a broad whistleblower statute, and many provisions do not contain a simple public-interest carveout.
That does not mean motives are irrelevant in the real world. They can affect charging discretion, negotiations, and sentencing arguments, even when they do not function as a formal defense at trial.
How courts manage the clash
This balancing is not a single test with one neat name. Instead, courts typically work through several recurring considerations.
- What exactly is the information? Courts look at whether it qualifies as national defense information and whether it was closely held.
- How did the defendant get it? Lawful access, unauthorized access, breach of duty, or receipt from someone else can affect the legal posture and the First Amendment arguments.
- What did the defendant do with it? Retaining, transmitting, disclosing to a third party, or failing to return can implicate different statutory provisions and different constitutional concerns.
- What mental state is required? Willfulness, knowledge, and intent shape the constitutional analysis by distinguishing negligent mistakes from deliberate violations.
- What is the claimed national security harm? Even when not a formal element, the government’s harm narrative often matters to how judges weigh competing interests and manage evidence.
Courts also confront practical problems that sit adjacent to the First Amendment: how to protect sensitive evidence during trial, how to avoid turning the courtroom into a disclosure engine, and how to preserve fair trial rights without forcing public release of secrets. In federal cases involving classified evidence, that management often runs through the Classified Information Procedures Act (CIPA), which sets procedures for substitutions, protective orders, and litigating what can be shown in open court.
Defendants, meanwhile, commonly test the statute’s edges through arguments such as vagueness, overbreadth, and disputes over whether the information truly qualifies as NDI.

Common misconceptions
“It only applies if you are spying for a foreign country.”
Some provisions require intent to harm the United States or aid a foreign nation. Others do not. Several modern charges focus on unauthorized possession, retention, or disclosure of national defense information without proving traditional espionage motives.
“If it was declassified, the Espionage Act cannot apply.”
Declassification is relevant, but the statute’s language centers on national defense information. Courts do not treat classification status as the only lens when assessing whether information falls within the statute.
“The First Amendment blocks all prosecutions involving publication.”
The First Amendment provides robust protection, especially against prior restraints. But it does not function as an all-purpose immunity for every act that results in information reaching the public. Courts often distinguish protected speech from unlawful acquisition, unauthorized retention, or disclosure in violation of legal duties. Historically, Espionage Act prosecutions have overwhelmingly targeted leakers and custodians of information, not the act of publication by mainstream outlets.
Why the law keeps returning
The Espionage Act endures because it sits at the intersection of three forces the Constitution must hold in the same hands:
- the government’s obligation to defend the nation,
- the public’s need to know what its government is doing, and
- the First Amendment’s refusal to let fear become a permanent censor.
It is not a tidy intersection. It is a recurring argument about what the republic can keep secret, what it must reveal, and who gets to decide the difference.
Quick glossary
- Espionage Act: a set of federal criminal provisions, commonly discussed through 18 U.S.C. §§ 793 to 798, covering espionage and unauthorized handling of national defense information (with related espionage provisions nearby in the criminal code).
- National defense information (NDI): a legal category referring generally to closely held defense-related information whose disclosure could harm U.S. national security or provide advantage to a foreign nation, as interpreted by courts.
- Willfully: acting intentionally rather than by accident, often with knowledge that the conduct violates a legal duty, with phrasing that can vary by statute and jurisdiction.
- Prior restraint: government action that blocks speech or publication before it occurs, heavily disfavored under First Amendment doctrine.
- CIPA: the Classified Information Procedures Act, which provides procedures for handling classified information in criminal cases.
